WiFi
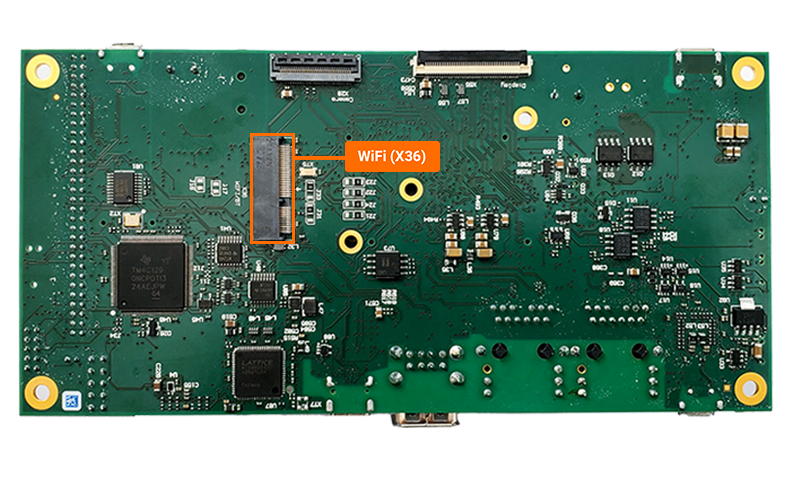
The phyCORE-AM62Ax development kit does not have WiFi integrated on the carrier board, but it can support external WiFi modules via the M.2 connector located on the bottom of the development kit carrier board, at X36. For more information on the M.2 connector on the phyCORE-AM62Ax development kit, please see the Hardware Manual.
Requirements
RF Antenna, 2.4GHZ/5GHZ (2069940100) Option 1
M2 4MM Bolt (Optional)
Warning
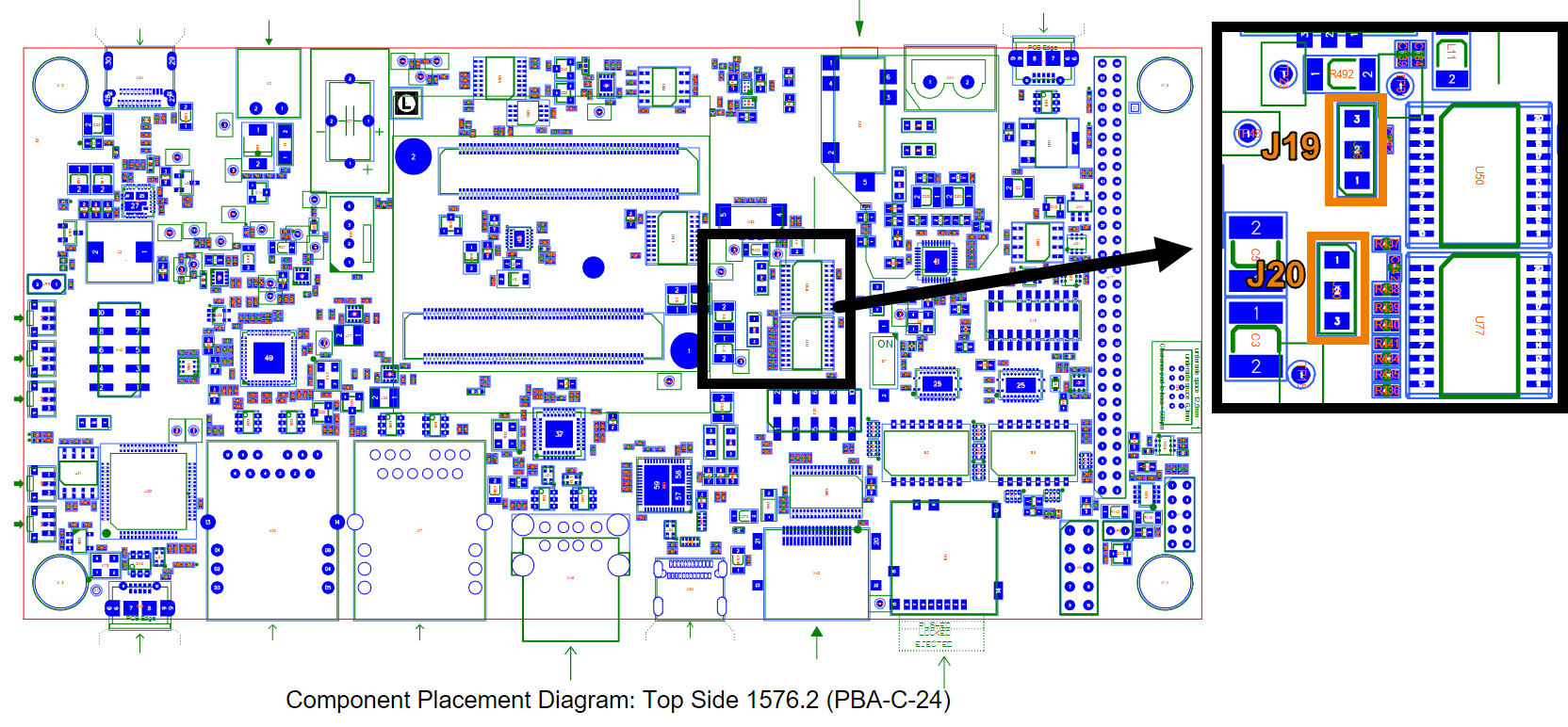
Depending on the WIFI module you are using, the jumpers J19 and J20 may require adjustment to level shift the signals routed out of the M.2 connector.
The module requires a 1.8V operating voltage, thus this module specifically requires J19 and J20 set to the 1+2 jumper position. This is the default position on the kit. (reference development kit schematics for clarification).
J19 |
1+2 = 1.8V |
2+3 = 3.3V |
Level shifts UART (Bluetooth) and PCM (audio) signals |
|---|---|---|---|
J20 |
1+2 = 1.8V |
2+3 = 3.3V |
Level shifts MMC (WIFI) signals |
Hardware Setup
Power off the development kit and disconnect the power supply.
Prepare the M.2 WiFi module by securing the antenna.
Connect the M.2 WiFi module to the X36 M.2 connector on the bottom side of the carrier board. We recommend securing the module with a M2 bolt into the soldered standoff.
Enabling the Firmware and Building the BSP (Yocto)
Warning
Attempting to use the LWB5+ Wifi module without setting the REGDOMAIN will result in the following error:
Direct firmware load for brcm/brcmfmac4373-sdio.phytec,am62a7-phyboard-lyra-rdk.bin failed with error -2
If you see the above error, you can use this section to select a regdomain. Otherwise skip to the “Enable the Bootloader Overlay” section of this wifi guide.
It is required that you select the region when building the BSP in order for the firmware to be included in the Image. Reference this Build the BSP guide to build the BSP image.
Set LWB_REGDOMAIN:
From the base Yocto directory we can edit our common.inc file as follows:
Host (Yocto BSP Build)vim sources/meta-ampliphy/conf/distro/common.inc
Un-comment the following line and update the region if necessary:
# Define Country Code for Laird LWB WiFi chips.
# Possible Codes: US/CA/ETSI/JP/AU/CN/TW/BR/KR
# ETSI includes all member countries of the European Union.
LWB_REGDOMAIN = "US" #<----- Uncomment this line
A list of regions is shown under Possible Codes for reference.
Rebuild the BSP and proceed.
Enable the Bootloader Overlay
The bootloader environment needs to be modified in order to enable the WiFi device tree overlay before booting into Linux. For more information on overlays please see section “Working with Overlays” of the guide Configuring the Bootloader.
Power on the development kit and hit any key to stop in U-Boot.
Target (U-Boot)setenv overlays k3-am62-phyboard-lyra-m2-lwb5p.dtbo boot
Note
For more information about overlays see the guide Configuring the Bootloader.
Configure WiFi Credentials
Once in Linux, scan for available networks:
Target (Linux)iw wlan0 scan | grep SSID
Example OutputSSID: OFFICE-GUEST SSID: OFFICE-5GWith a network identified, use wpa_passphrase to create the NETWORK section of your wpa_supplicant-wlan0.conf file with your network credentials and password fille in:
Note
Update “MYSSID” and “passphrase” to the correct credentials for your target network.
mkdir -p /etc/wpa_supplicant
wpa_passphrase MYSSID passphrase > /etc/wpa_supplicant/wpa_supplicant-wlan0.conf
Now we can edit the wpa_supplicant-wlan0.conf to include the rest of our network configuration.
Target (Linux)vi /etc/wpa_supplicant/wpa_supplicant-wlan0.conf
Note
The vi text editor begins in “Command Mode” and you must first hit the ‘i’ key in order to enter “Insert Mode”. Using the arrow keys to navigate, make the necessary changes and then hit ESC to go back to “Command mode”. Now enter “:wq” to write the file and quit.
Pro Tip: Use the right click on your mouse to paste! This will only work if you are in “Insert Mode” first.
# Giving configuration update rights to wpa_cli
ctrl_interface=/var/run/wpa_supplicant
ctrl_interface_group=0
update_config=1
# AP scanning
ap_scan=1
# ISO/IEC alpha2 country code in which the device is operating
country=US
# network section generated by wpa_passphrase
network={
ssid="OFFICE-GUEST"
#psk="123456"
psk=59e0d07fa4c7741797a4e394f38a5c321e3bed51d54ad5fcbd3f84bc7415d73d
}
Establish A Connection
Enable the wpa_service for the wlan0 interface:
Target (Linux)systemctl enable wpa_supplicant@wlan0.service
Restart the systemd-networkd and wpa_supplicant services:
Target (Linux)systemctl restart systemd-networkd.service systemctl restart wpa_supplicant@wlan0.service
Confirm wlan0 is connected to the network.
Target (Linux)iw dev wlan0 link
Expected OutputConnected to 6e:d7:9a:cd:92:e9 (on wlan0) SSID: OFFICE-GUEST freq: 2437 RX: 3684015 bytes (18198 packets) TX: 57638 bytes (745 packets) signal: -88 dBm rx bitrate: 39.0 MBit/s tx bitrate: 6.0 MBit/s bss flags: short-preamble short-slot-time dtim period: 1 beacon int: 100
Check the IP address:
Target (Linux)ip addr show wlan0
Expected Output5: wlan0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000 link/ether c0:ee:40:84:4e:ec brd ff:ff:ff:ff:ff:ff inet 100.55.50.55/24 metric 1024 brd 100.55.50.255 scope global dynamic wlan0 valid_lft 70512sec preferred_lft 70512sec inet6 fe80::c2ee:40ff:fe84:4eec/64 scope link valid_lft forever preferred_lft foreverIn the above example output we can see that this system has been assigned the 100.55.50.55 IPv4 address.
Verify that the M.2 WiFi module connected to the network.
Target (Linux)ping -c 5 -I wlan0 google.com
Expected OutputPING google.com (142.251.33.110): 56 data bytes 64 bytes from 142.251.33.110: seq=0 ttl=56 time=464.257 ms 64 bytes from 142.251.33.110: seq=1 ttl=56 time=13.316 ms 64 bytes from 142.251.33.110: seq=2 ttl=56 time=15.097 ms 64 bytes from 142.251.33.110: seq=3 ttl=56 time=13.265 ms 64 bytes from 142.251.33.110: seq=4 ttl=56 time=13.039 ms --- google.com ping statistics --- 5 packets transmitted, 5 packets received, 0% packet loss round-trip min/avg/max = 13.039/103.794/464.257 ms